Overview
The Authorizer is an open source authorization engine which uses the Open Policy Agent (OPA) to compute a decision based on a policy, user context, and data.
An application can interact with the Authorizer through a set of gRPC or HTTPS REST APIs.
gRPC API documentation
The gRPC APIs are described here.
REST API documentation
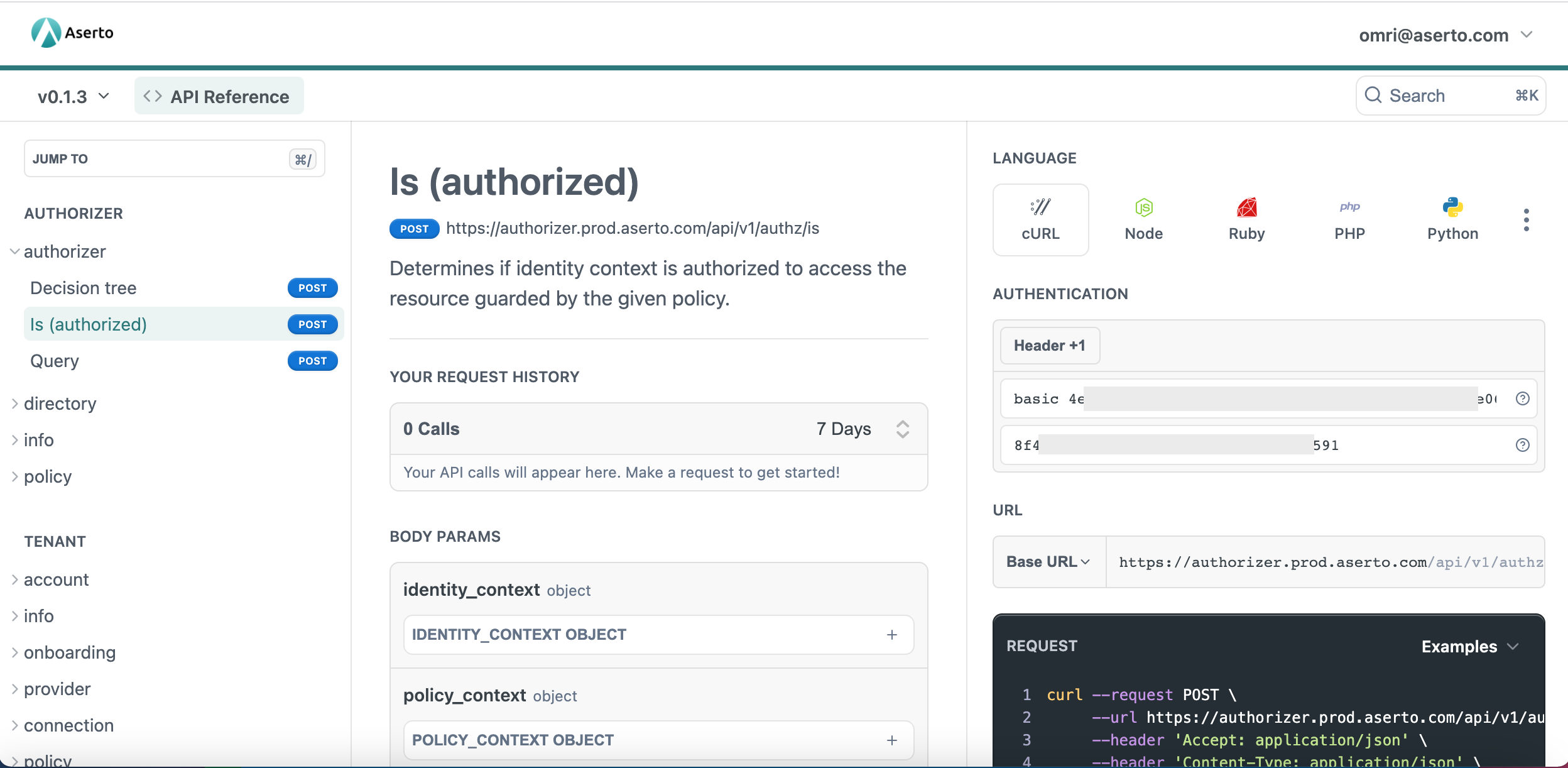
The Aserto Authorizer APIs are documented here. They are generated from the OpenAPI specification of each of the APIs, and and are meant to be used as the definitive reference for the Authorizer API surface.
If you have an Aserto account, sign in to the console, and
select the API Docs menu item. This will bring up an authenticated experience for the
reference docs, and automatically fill in the current Tenant ID, authorizer API key, and JWT
so that you can directly execute API calls from the dashboard.
Hosted Authorizer vs Edge Authorizer
Creating an Aserto tenant automatically creates a corresponding Authorizer instance in the multi-tenant hosted Authorizer. Since it's a multi-tenant service, the hosted Authorizer requires authorization headers to disambiguate the tenant and provide the tenant secret (API key).
The Aserto authorizer can also be deployed as a sidecar (or as a local service), right next to your application. Since this Authorizer is a single-tenant service, it does not require authentication, besides the certificate validation mandated by HTTPS mutual TLS.
Authorization
Any API call to the hosted Authorizer requires two HTTP headers:
Aserto-Tenant-ID: <Tenant-ID>Authorization: basic <Authorizer-API-Key>
You can find these values in the Policy settings in the Aserto Console.
Authorizer API categories
The Authorizer provides the following API categories to calling applications:
- Authorization (
authz) - Policy (
policy) - Information (
info)
The v1 Directory (dir) namespace is now deprecated in favor of the v2 Directory graphQL APIs.
The v1 System (sys) namespace is now removed from v2.